Compliance Strategy: Institutional Transformation
DPDP Act: Operational Realities
Section titled “DPDP Act: Operational Realities”The implementation of the Digital Personal Data Protection (DPDP) Act, 2023 represents a monumental shift for Indian healthcare. As Bagmisikha Puhan (Associate Partner, TMT & Digital Health Legal) details, privacy is no longer an option; it is a Fundamental Right.
The Digital Personal Data Protection (DPDP) Act is a workflow disruptor. Since every discrete data point in a hospital involves personal health information, compliance impacts every aspect of management—from front-desk registration to clinical discharge.
The High Stakes of Compliance
Section titled “The High Stakes of Compliance”The Act introduces a regime of Heavy Penalties specifically targeting Breach Liability. Hospitals must now navigate substantial procedural norms, from Breach Reporting and Grievance Redressal to maintaining a robust Regulatory Architecture.
Core Challenges for Hospitals
Section titled “Core Challenges for Hospitals”- Personal Data & Scanned Documents: Under DPDP, “Personal Data” is any identifier that can pinpoint an individual, either by itself or in conjunction with other data sets. Crucially, the Act applies to data collected in digital form or collected in non-digital form and digitized subsequently (the “Scanned Document” rule).
Regulatory Risk: The “Dual Penalty” Threat
Section titled “Regulatory Risk: The “Dual Penalty” Threat”Non-compliance in a digitized environment carries a double-edged risk. A data breach doesn’t just trigger one investigation; it triggers two:
graph TD A["Data Breach Incident"] A --> B["Track 1: Sectoral (ABDM/NHA)"] A --> C["Track 2: National (DPDP Act 2023)"]
B --> B1["Violates HDMP"] B1 --> B2["Penalties & Blacklisting"]
C --> C1["Violates National Law"] C1 --> C2["Financial Penalties (up to ₹250 Cr)"]
B2 & C2 --> D["Institutional Survival Risk"]
style A fill:#fce4ec,stroke:#d81b60 style B fill:#e3f2fd,stroke:#1e88e5 style C fill:#fff3e0,stroke:#fb8c00 style D fill:#f5f5f5,stroke:#333,stroke-width:2px- Sectoral Penalty: Penalties and blacklisting under the ABDM/National Health Authority (NHA) framework for violating the Health Data Management Policy.
- National Penalty: Massive financial penalties (up to ₹250 Crores) under the DPDP Act 2023 for failure to protect personal data.
Data Protection: Clinical Best Practices (Speaker: Ms. Bagmisikha Puhan)
Section titled “Data Protection: Clinical Best Practices (Speaker: Ms. Bagmisikha Puhan)”Implementing a resilient privacy framework requires moving from policy to practice. The following 8-pillar framework defines the gold standard for clinical data protection under the DPDP Act:
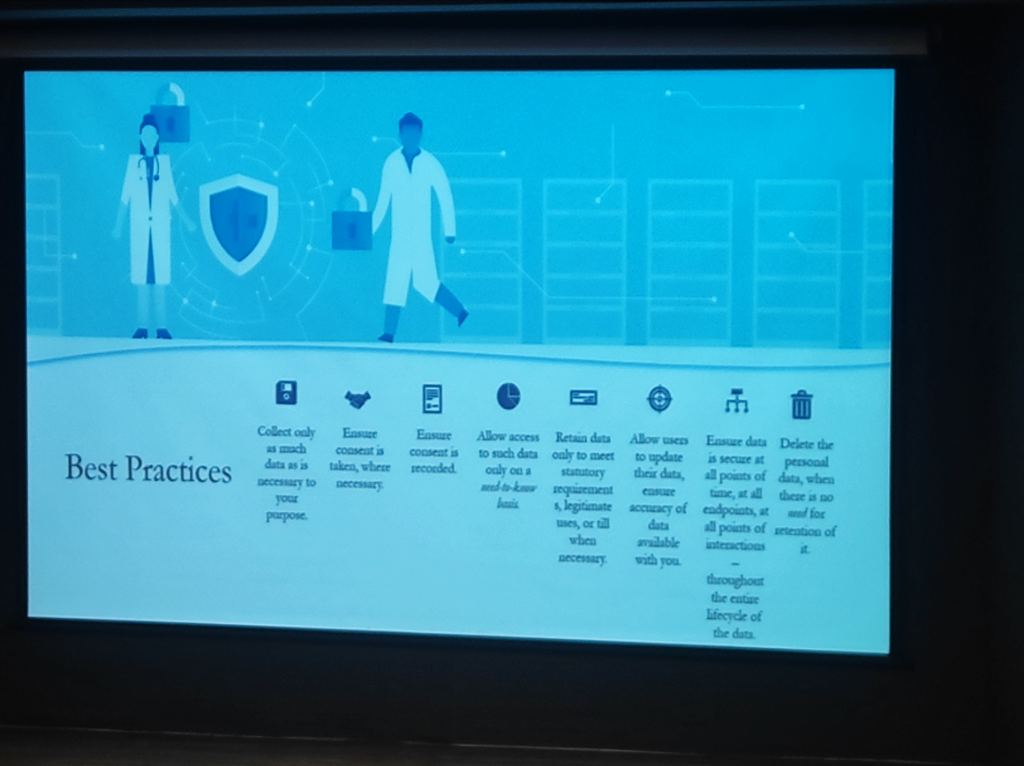 Figure: The 8-pillar framework for clinical data protection—ensuring privacy at every stage of the data lifecycle.
Figure: The 8-pillar framework for clinical data protection—ensuring privacy at every stage of the data lifecycle.
- Strict Data Minimization: Collect and process only as much data as is strictly necessary for the purpose.
- Recorded Consent: Ensure that every piece of patient data is backed by recorded, unbundled consent.
- Need-to-Know Access: Restrict access to patient files only to users who have a legitimate clinical or administrative requirement.
- Lifecycle Security: Ensure data is secure at all points of interaction—from capture to archive.
- User-Driven Accuracy: Allow patients to update or verify their information, ensuring clinical record integrity.
- Statutory Retention: Retain data only as long as required by law (e.g., IMC 2002 regulations).
- Timely Deletion: Permanently delete personal data when there is no further clinical or legal need (Right to Erasure).
- Accountability & Auditing: Maintain logs and conduct regular audits to ensure effective observance of privacy standards.
Annual Governance Audits
Section titled “Annual Governance Audits”Hospitals must conduct a mandatory annual audit specifically targeting Data Deletion, Retention policies, and Purging schedules to ensure technical execution matches clinical and legal mandates.
Governance & The “CSO Gap”
Section titled “Governance & The “CSO Gap””As Vinayak Godse (CEO, Data Security Council of India - DSCI) emphasizes, the cybersecurity landscape in healthcare is significantly behind other regulated sectors.
- The CSO Absence: Unlike the financial sector, where the Chief Security Officer (CSO) is a mandatory and institutionalized function, most Indian hospitals lack a dedicated leadership role for cybersecurity. Security is often treated as an “IT side-task” rather than a core governance pillar.
- The Banking Comparison: In banking, the RBI has established a rigorous framework that mandates security posture, response protocols, and continuous auditing. Healthcare requires a similar shift from passive protection to active, regulated cybersecurity governance.
- Fragmented Infrastructure Risks: The “fragmented” nature of hospital infrastructure—from legacy on-prem servers to unmanaged medical devices—creates significant data protection gaps and increases vulnerability to ransomware.
- Continuous Posture Improvement: Post-AIIMS, the message is clear: security is not a “fire-and-forget” solution. It requires a continuous improvement of architecture, posture, and response capabilities to stay resilient against evolving threats.
DPDP Act: Challenges and Response (Speaker: Ms. Bagmisikha Puhan)
Section titled “DPDP Act: Challenges and Response (Speaker: Ms. Bagmisikha Puhan)”The transition to a DPDP-compliant culture requires a strategic shift from passive compliance to active risk and engagement management.
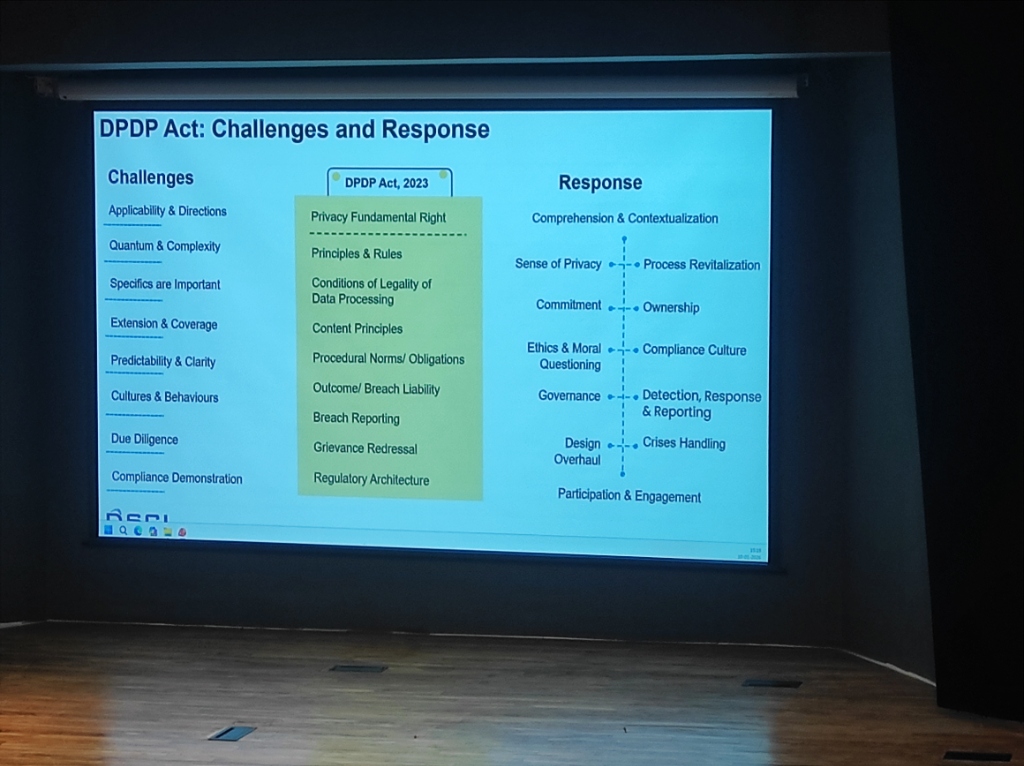 Figure: The strategic roadmap for DPDP Act implementation—transforming institutional culture.
Figure: The strategic roadmap for DPDP Act implementation—transforming institutional culture.
- Challenges: Navigating applicability, quantum/complexity of data, and specific procedural norms.
- Response: Orchestrating comprehension, process revitalization, and institutional ownership.
The DPO & The Cultural Shift
Section titled “The DPO & The Cultural Shift”A critical component of this legal architecture is the Data Protection Officer (DPO). However, the role faces unique challenges in the Indian context:
- The Query Gap: Currently, DPO-related questions and scrutiny are significantly more mature and frequent outside India. International users and regulators demand more granular data handling details than domestic entities.
- Social Economy & Culture: Privacy governance in India is deeply influenced by our unique social economy and culture. Unlike Western-centric models, Indian privacy must account for a transition from a community-based data sharing culture to a strictly regulated individual rights model.
- From Paper to Practice: Compliance is shifting from “filling forms” to managing real-time data rights. This requires a cultural shift where the DPO is not just a legal signatory but a core part of the hospital’s clinical and digital workflow.
Insurance & TPA: The Neglected Security Gap
Section titled “Insurance & TPA: The Neglected Security Gap”The processing of Insurance Claims and TPA (Third-Party Administrator) interactions remains one of the most neglected areas of data security in Indian healthcare:
- Neglected Security Protocols: While internal clinical systems are increasingly secured, the data sent to insurers often lacks rigorous security SOPs.
- Unsafe Sharing Habits: Sensitive patient claims data is frequently shared through unmanaged, unsecured channels, creating massive exposure risks for both the patient and the hospital.
- The Compliance Gap: Under DPDP, the hospital remains the primary Data Fiduciary—liable for how the patient’s data is handled even when it leaves the premises for insurance processing.
Vendor & Medtech: The Supply Chain Blind Spot
Section titled “Vendor & Medtech: The Supply Chain Blind Spot”The technical ecosystem of a modern hospital involves dozens of third-party Medtech and software vendors. These represent a major “blind spot” in security governance:
- Supply Chain Vulnerabilities: As seen in global attacks, hackers often target smaller vendors to gain a foothold in larger hospital networks.
- Unmanaged Vendor Access: Allowing vendors “always-on” or unmonitored remote access to clinical systems is a high-risk practice.
- Mandatory Risk Assessments: Institutions must mandate periodic Third-Party Risk Assessments (TPRA) and enforce Least-Privilege Access for all Medtech partners. Managed connectivity (via secure VPCs or ZTNA) is non-negotiable for vendor integrations.
- Contractual Liability: Security is not just technical; it’s legal. Vendor contracts must explicitly define breach liability and security standards alignment.
