Security Architecture & Threats (Speaker: Mr. Vinayak Godse, CEO, DSCI)
🛡 Galaxy — National Cybersecurity Governance & Clinical Resiliency.
A core strategic pillar of the digital health mission is the multi-layered protection of clinical and personal data. As Vinayak Godse (CEO, DSCI) details, this moves beyond simple firewalls into a robust architecture of encryption and access control.
The Security Lifecycle
Section titled “The Security Lifecycle”graph TD subgraph "Data at Rest (Static)" A["Hospital Servers / Cloud DB"] --> B["AES-256 bit Encryption"] B --> C["Encrypted Storage Media"] end
subgraph "Data in Transit (Motion)" D["Sender (Hospital/HIS)"] --> E["TLS 1.3 / SSL Tunnel"] E --> F["Receiver (ABDM/HIE)"] end
subgraph "Access Control (Governance)" G["Identity Verification"] --> H["Role-Based Access (RBAC)"] H --> I["Authorized Clinical Review"] end
C -.-> D F -.-> G
style B fill:#e3f2fd,stroke:#1e88e5,stroke-width:2px style E fill:#e8f5e9,stroke:#43a047,stroke-width:2px style H fill:#fff3e0,stroke:#fb8c00,stroke-width:2pxKey Security Pillars
Section titled “Key Security Pillars”- Data at Rest: Diagnostic reports and medical images must be secured using AES-256 bit Encryption to ensure data remains unreadable if storage media is compromised.
- Data in Transit: Patient data shared with national backbones like ABDM must be protected using TLS 1.3 / SSL to prevent “man-in-the-middle” attacks.
- DMZ (Demilitarized Zones): Acts as a security buffer, allowing external communication (via VPCs) without exposing core clinical databases.
- RBAC (Role-Based Access Control): Ensures that only authorized personnel can access specific pillars of a patient’s medical history.
- Compliance & Audit: Regular automated security audits are mandatory to maintain long-term trust in “my hospital data.”
Global Health Data Security Standards
Section titled “Global Health Data Security Standards”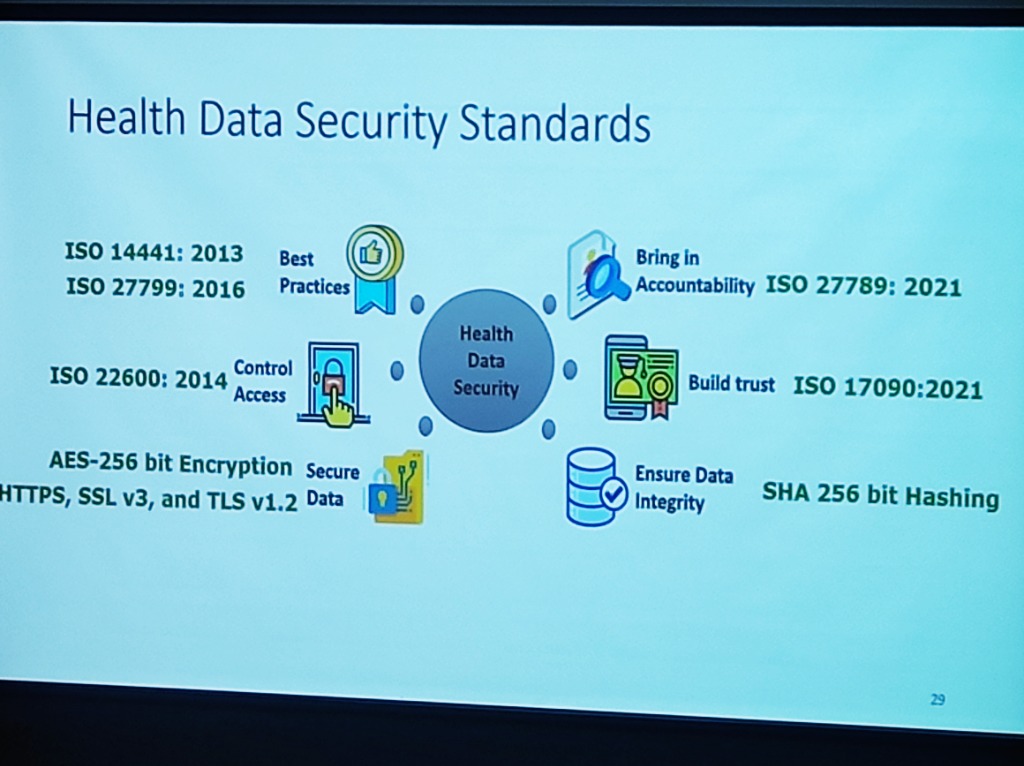 Figure: The global landscape of health data security standards—from ISO best practices to high-fidelity encryption.
Figure: The global landscape of health data security standards—from ISO best practices to high-fidelity encryption.
A resilient security architecture must align with international benchmarks:
- Best Practices: Adhering to ISO 144441:2013 and ISO 27799:2016 for information security management in health.
- Access Control: Managing semantic interoperability and trust through ISO 22600:2014.
- Data Integrity: Utilizing SHA 256 bit Hashing to ensure that data has not been tampered with during transit or storage.
- Accountability: Bringing in technical accountability through ISO 27789:2021 (audit trails).
- Encryption Standards: Mandating AES-256 bit Encryption and TLS v1.2+ for “on-wire” and “at-rest” security.
Implementing Technical Measures: A 4-Pillar Roadmap
Section titled “Implementing Technical Measures: A 4-Pillar Roadmap”To counter these evolving threats, institutions must move from theoretical security to a rigorous technical implementation roadmap:
- Restrict Access & Multi-Factor Authentication (MFA): Access must be strictly limited to authorized users only. Implementing Multi-Factor Authentication (MFA) across all clinical and administrative applications is non-negotiable for securing HIS entry points.
- Periodical Risk Assessments: Security is dynamic. Hospitals must conduct regular risk assessments to identify technical vulnerabilities, internal loopholes, and the security posture of third-party vendors and service providers.
- Data Encryption at Scale: Comprehensive Data Encryption must be enforced throughout the information lifecycle—securing data both In Transit (across networks) and At Rest (on storage servers).
- Anonymization & Aggregation: To further mitigate re-identification risks, hospitals should utilize aggregated datasets which significantly decrease the chances of a specific individual being pinpointed from a larger data set.
Threat Vectors in Healthcare
Section titled “Threat Vectors in Healthcare”The risk landscape in healthcare has evolved into a multi-layered challenge. As per DSCI’s analysis, these threats can be categorized into three distinct tiers:
- Primary Threats: Foundational risks including Phishing and Social Engineering, Ransomware and Malware, Data Breaches, Credential Stuffing, and Insider Threats (both negligent and malicious).
- Advanced & Complex Threats: Highly targeted attacks such as API Exploits, Supply Chain/Vendor Compromise, Compromised IoMT (Internet of Medical Things), Zero Day Exploits, and Shadow IT/AI.
- Emerging & Uncertain Threats: The next generation of risks featuring AI-Assisted Attacks, Quantum Risk, and Adversarial AI.
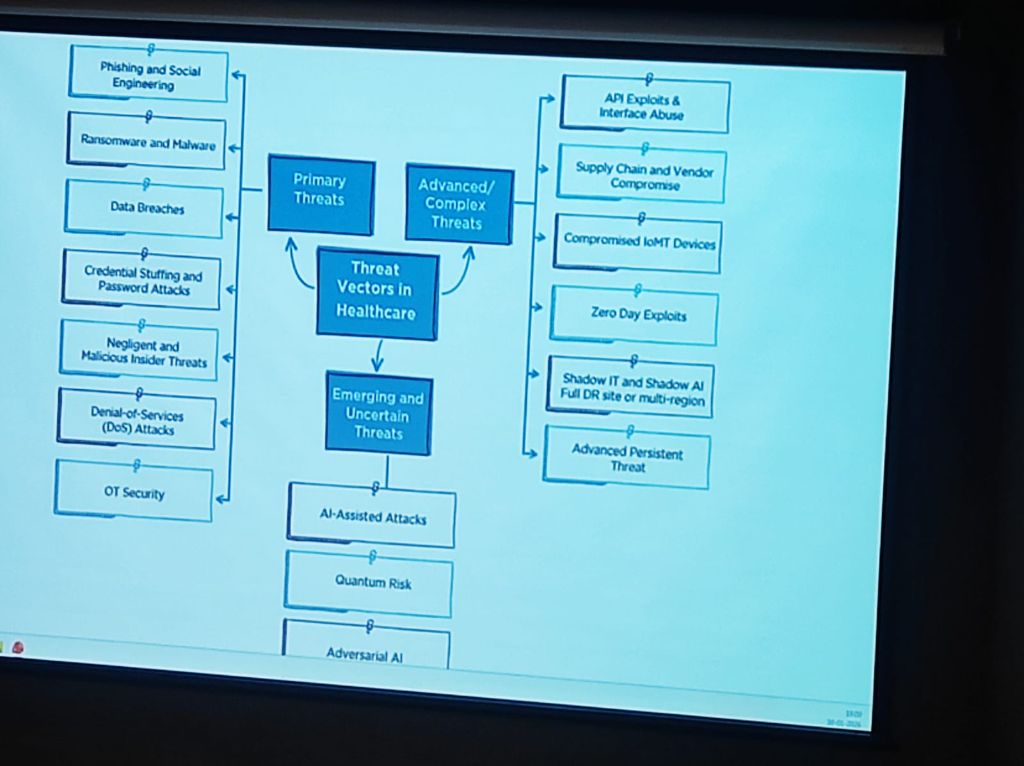 Figure: The evolving landscape of threat vectors in healthcare—from primary breaches to emerging quantum and AI risks.
Figure: The evolving landscape of threat vectors in healthcare—from primary breaches to emerging quantum and AI risks.
Ransomware Advancements
Section titled “Ransomware Advancements”Ransomware attacks in healthcare are no longer just about encryption; they have become highly advanced technical operations:
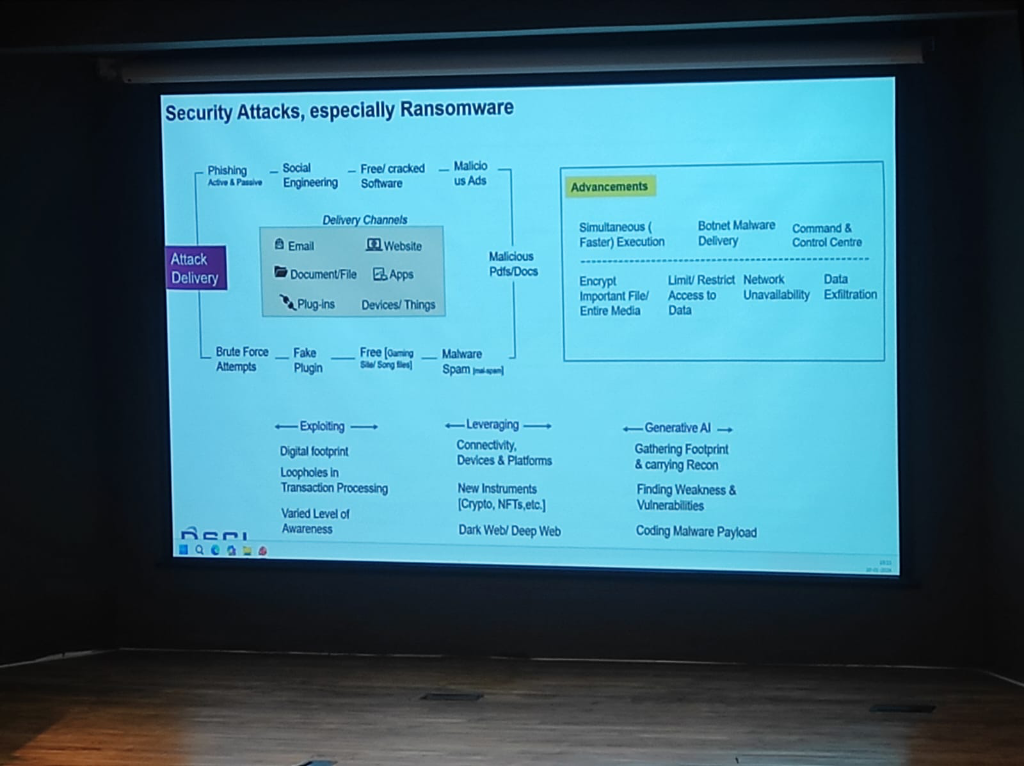 Figure: The technical advancements in ransomware delivery and the role of Generative AI in lowering the barrier for clinical exploitation.
Figure: The technical advancements in ransomware delivery and the role of Generative AI in lowering the barrier for clinical exploitation.
- Simultaneous Execution: Modern ransomware executes faster across entire networks, encrypting important files and media simultaneously to prevent manual intervention.
- Botnet & Malware Delivery: Attackers use sophisticated Botnet delivery channels and Command & Control (C2) centers to automate the exfiltration of sensitive patient records.
- The Gen-AI Lowering the Bar: Generative AI has made exploitation easier than ever. It enables attackers to gather footprints, find vulnerabilities, and code malicious payloads with minimal specialized effort.
A Shared Ecosystem Mandate
Section titled “A Shared Ecosystem Mandate”This heightened risk requires a unified awareness across the entire ecosystem. Health Providers, Medtech companies, Government agencies, and Insurance providers must all adopt a “Response & Recovery” first mindset to stay resilient against the next generation of cyber threats.
The WhatsApp Vulnerability: A Real-World Sentiment
Section titled “The WhatsApp Vulnerability: A Real-World Sentiment”The pervasive use of consumer messaging apps like WhatsApp for clinical data exchange represents the single largest security “blind spot” in the ecosystem. To gauge the depth of this practice, KCDH conducted a live audience poll.
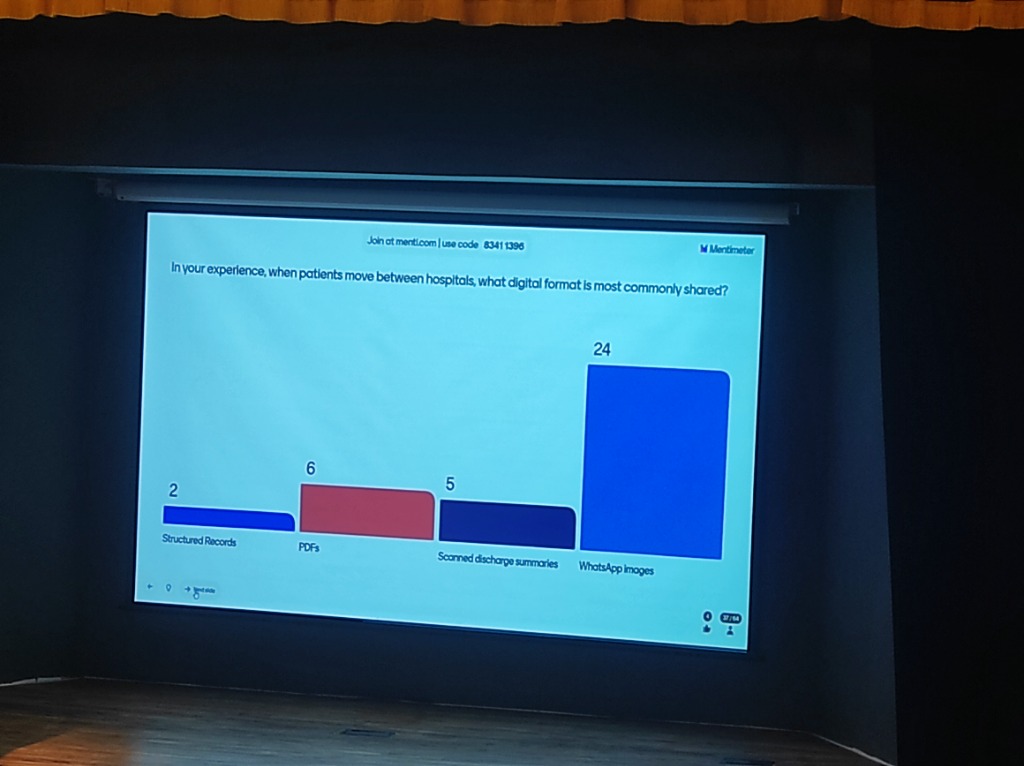 Figure: Live Audience Poll: “When patients move between hospitals, what digital format is most commonly shared?” — Highlighting the massive dominance of unprotected WhatsApp images over structured records.
Figure: Live Audience Poll: “When patients move between hospitals, what digital format is most commonly shared?” — Highlighting the massive dominance of unprotected WhatsApp images over structured records.
- The Data Reality: Over 65% of participants identified WhatsApp as the primary sharing medium, compared to negligible usage of structured digital records.
- Zero Audit Trails: Unlike institutional EMRs, consumer apps provide no standardized logs of who accessed what data and when, making forensic analysis impossible after a breach.
- DPDP Non-Compliance: Sharing personally identifiable health information (PII/PHI) on unmanaged consumer platforms is a direct violation of the DPDP Act. The institution—not the app provider—remains liable for the data leakage.
- The “Shadow Data” Problem: Once a medical report is shared on WhatsApp, it exists in an unmanaged, unencrypted-at-rest state on personal devices, bypassing all institutional security perimeters.
Managed Security Architecture & Observability
Section titled “Managed Security Architecture & Observability”The convergence of rising Quantum complexities, high-velocity data exchanges, and deep cloud dependencies mandates a shift in how hospital architectures are managed:
- Managed Security Architecture: Security is no longer a perimeter firewall; it is a feature of the data flow itself. Architecture must be managed dynamically to counter API exploits, zero-day vulnerabilities, and adversarial AI.
- The Observability Requirement: Hospitals must allocate dedicated budgets for Monitoring and Observability systems. These platforms provide real-time visibility into the “health” of the data ecosystem—detecting anomalies, unauthorized access, and system latencies before they impact patient care.
- Data Flow Integrity: As hospitals become nodes in a national data exchange, observability ensures that every “Scan and Share” or FHIR transaction is secure, audited, and performing at clinical-grade speeds.
Security: Problem Management & Response (Speaker: Mr. Vinayak Godse)
Section titled “Security: Problem Management & Response (Speaker: Mr. Vinayak Godse)”The strategy for protecting medical data has evolved from passive assessment to real-time management and multi-dimensional resiliency. This requires a shift in how institutions handle technical and procedural threats.
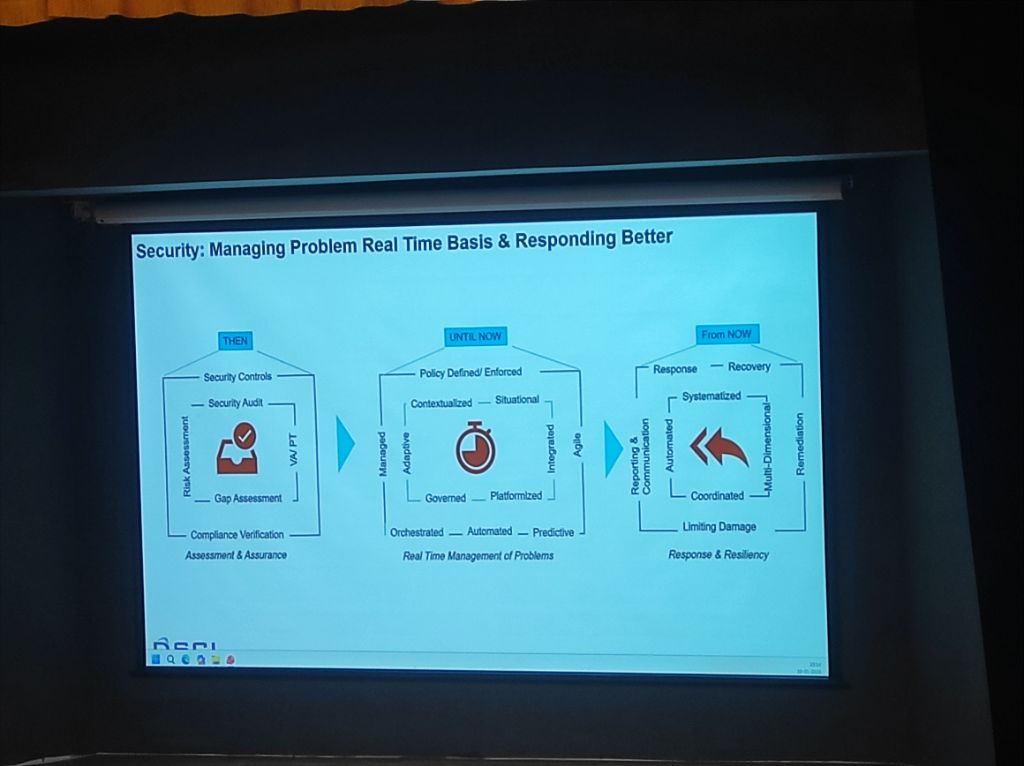 Figure: The evolution of clinical security—Managing problems on a real-time basis and responding better.
Figure: The evolution of clinical security—Managing problems on a real-time basis and responding better.
- THEN (Assessment & Assurance): Focus on static controls, audits, and compliance verification.
- UNTIL NOW (Real-Time Management): Shift toward contextualized, platformized, and agile problem management.
- FROM NOW (Response & Resiliency): Reaching multi-dimensional resiliency through coordinated, automated, and systematized response.
